For attackers and defenders, tools are very important. If a threat actor does not know much about a potential target, they will need to perform some reconnaissance. There are many tools out there that can be leveraged for recon, some of which are readily available on popular operating systems. These tools are not necesarily built with a purpose of reconnaissance as a goal, but they can be used that way. One way for a threat actor to find out more about a target domain is by levearaging the Domain Name System (DNS). There are many different types of DNS records that can provide some insight about what a potential target has on their network. By nature of systems that leverage TCP/IP, computers need to be able to find out the IP addresses of the destination systems with which they are attempting to communicate. At a high level, DNS is used to translate familiar names into IP addresses, in a client/server model. This keeps us humans from having to memorize IP addresses of websites and the like, keeping both private and public networks (the internet) usable and dynamic. Tools such as nslookup (Windows), dig (Linux), and dnsenum can be used to query DNS servers to gather information about domains.
Now, let’s take a look at the nslookup utility within Windows to see what some of the options are that exist within the tool. First off, to run nslookup, just open up a command prompt, type nslookup and hit the enter key. This will take you into the nslookup prompt. First, we can look at the existing settings within the utility using the set all command.
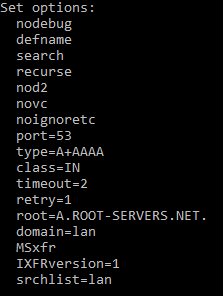
An option of note listed above is the type option. This sets the type of query that will be performed. You can see above that it is currently set to the default of A+AAAA, so it will query for IPv4 and IPv6 A records. The available options are: A,AAAA,A+AAAA,ANY,CNAME,MX,NS,PTR,SOA,SRV. To change the record type, you can enter set type=<record type>. Another option, that could be potentially used for reconnaissance is the all type. If you enter set type=all (then hit enter), then enter a domain name to query; if the server allows it, it will return the answers of all records in that DNS zone. This type of query can be thought of as a zone transfer.
Once the settings are configured the way you want them (oftentimes they can be left default if you are just wanting to query basic A records), you are just about ready to query a domain name. Sometimes, when it comes to troubleshooting potential DNS issues, perspective is key. When record changes are made, especially to public facing DNS servers, by nature of time-to-live (TTL) values, it can take ptotentially a considerable amount of time for a record to change to reach global DNS propagation. You may want to query different local or public DNS servers to see how they are resolving the record in question. That could explain why a record is resolving correctly for some users that point to DNS server #1 and incorrectly for other users that point to DNS server #2. Within nslookup, to change the server you want to query, you just type server followed by a space, followed by the IP address of name of the DNS server that you want to query (then hit enter). Finally, to query a record, you just have to type in the name of the record (as a fully qualified domain name) and hit the enter key. If the DNS server you are pointing to is able to resolve this record to an IP address, you will the result on the screen.
Leveraging DNS query tools such as nslookup, dig, and dnsenum can absolutley be used as methods of gathering reconnaissance by threat actors. Having a list of records from a target domain could give the threat actor information about services the target is running, or in the least, a list of devices to scan for open services and/or vulnerabilities.
